Why Cybersecurity is important for Small and Medium Businesses (SMBs)?

What is cyber security?
Firms operate and conduct their business transactions in a virtual space. Since all activities are performed in cyberspace, it becomes imperative to protect the business interests like services, networks & equipment from all threats. This discipline is called ‘Cyber security.
A good cyber security system prevents any form of malice by denying unauthorized access to any form of instrument. Businesses that understand their significance can protect their customers and their assets. The rest become easy prey at some time in the business conduct.
Why are small businesses vulnerable to cyber attacks?
In today’s world, wherever there is data and digitalization, they become targets of cyber attacks. The threat of cyber-attacks comes to the forefront only when large industries become their victims and catch the eyeballs of millions of people. Whereas any form of a security breach to smaller firms never reaches the headlines. Therefore, exposure to the right information and ignorance from the owners of SMBs give cyber attackers a haven to launch their strikes.
According to IBM Small and mid-sized businesses are hit by 62 percent of all cyber-attacks, about 4,000 per day. To add more to the injury, 60% of small companies run out of business within six months.
Let us understand the reasons why SMBs become potential victims.
1. State of denial
According to a Bullguard research survey 60% of SMB firms’ partners or owners firmly believe their firms can never be targets of cybercriminals. This denial is worrisome as they risk their firms’ prospects and simultaneously risk the confidential data of firms/employees doing business or working under them.
2. Unchecked freeway
Large organizations generally connect with numerous small firms in doing business. SMBs are typically given access to log in to larger firms’ domains. Hackers tend to utilize the vulnerabilities of security of small firms to target the larger firms as it gives them a ‘freeway’ to dive into their records & credentials. This security lapse ruins the SMBs’ reputation and strains the financial benefits.
3. Restricted cash flow
SMBs do not have the luxury of spending a hefty budget on cyber security.
Ponemon Institute survey shows that a staggering 35% of SMBs say IT security priorities never feature in their function. While there is no allocation of funds in their limited budget, these firms have become a hotspot for cyber theft.
4. Deficiency in training
While SMBs spent their valuable time and resources on the various elements of their business to remain in a cut-throat environment. Unfortunately, they do not provide the necessary training to their staff. Therefore, without any reservation, it can be noted that 95% of the breach in security is due to human negligence. The blame game is no one’s fault except themself.
If some time is spent on training the employees, e.g., not to open unknown email attachments and never to download any unauthorized software, things will remain better on the ground.
5. Literacy of work from home
The demand and the necessity during Covid brought a new culture of ‘Work from home’. Though it is beneficial for the well-being of the employer/employee, there is a lot of security lapse due to this policy. According to Knowbe4.com, Data Breach Costs Increase by $1 Million When Remote Workers Are Involved.
When the concept of ‘work from home’ is going to be the future, steps need to be taken to educate employees about the perils of malware attacks.
What are the common cybersecurity threats to small businesses?
Cyber attackers are traders who are out to make a ‘fast buck. Without a doubt, it is a lucrative market.
As per the Accenture survey Forty-three percent of cyberattacks are aimed at small businesses, but only 14% are prepared to defend themselves.
Irrespective of the sizes, there is an average loss of $200,000 per Insurance co Hiscox.
What is at stake for these SMBs due to these cyber threats? Once your firm is under cyberattacks, everything built for years by the firm is now at its mercy.
- Financial information, including access to your bank accounts.
- Nature of business and their associates.
- Confidential database internal and external
To enhance awareness, let us discuss some of the threats below
1. Simple password
The most common threat comes in the form of a weak password. Businesses use multiple platforms for conducting their WorkWork and have to log on to various servers. For convenience, they make the grave mistake of using identical passwords for all the platforms at Work. Even the stronger password is compromised when the same password is shared amongst colleagues across a common work platform.
Cybercriminals have various ways of cracking your password using the common passwords enlisted in the password dictionary. Another way is ‘a brute force attack where keywords are combined using your social media personnel information shared like family members’ birthdays’, anniversaries, and favorite items.
2. Phishing
The most widespread way of intrusion is phishing. The criminal’s main aim is to get access to your personal information like bank accounts, social security numbers, and passwords.
To gain the trust of the individuals, they send through your email handle links for downloading for log-in purposes, attachment files to open so forth.
Since this form of cyber theft is through the human element rather than technology, the penetration can be curtailed by properly creating awareness among staff members.
3. Malware
This is a common phrase used for software designed to execute unauthorized and malicious actions in the system or network. The hacker very tactfully deploys the software either through phishing or ransomware and slowly allows the malware to start functioning.
Some of the common and well known are
- Trojan horse – it is hidden in the application as a game.
- Worm and virus– coded to replicate itself and infects both the system and other programs.
- Spyware – designed to transmit all activities in your system to the hacker.
4. Ransomware
The word ‘Ransom’ is synonymous with kidnapping individuals and extorting money from them. The idea is the same here; the victim is the firms’ encrypted data. Criminals know smaller firms do not have a sophisticated system for data backup. The criminals seek a handsome amount to retrieve and unlock the data. From records, it is understood that nearly 71% of Ransomware Attacks Targeted Small Businesses in 2018.
Ransomware is the final crusade in the cyberattack process. Once they access the company network through malware, they deploy ransomware to access the entire network system.
How to secure your business from cybersecurity threats?
Digitalization is happening, and whether we buy into the idea or not, we must conduct our business online. As the proverb says, ‘Be a Roman when in Rome”. Despite the various cybercrimes, we have to secure our place of WorkWork and systems to defeat the intruders’ purpose. So how do we do it?
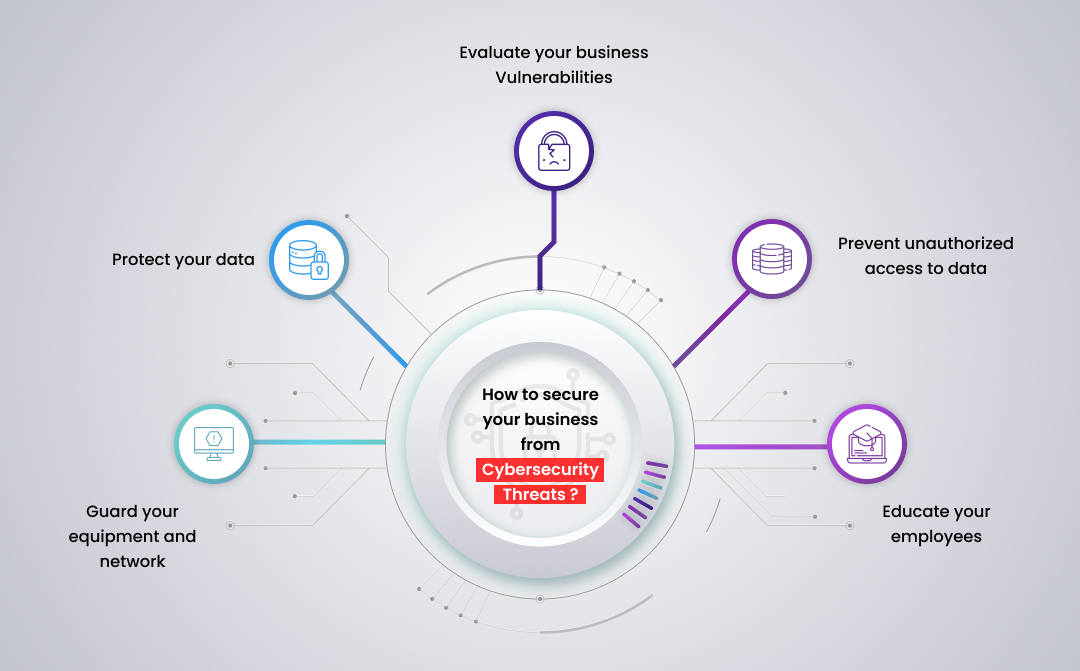
a. Evaluate your business vulnerabilities
Self-assessment is the best appraisal for a business establishment.
- We must check-list all the equipment generating data and their connectivity to cyberspace.
- Assess how the current security system can handle the influx of cyber criminals.
b. Prevent unauthorized access to data
Employees should have access to information limited to their job description and per hierarchical structure. If, in case, the employee is transferred to another department, their privilege in the present set-up should be immediately curtailed.
When leaving the firm, their log-in access should be stopped immediately.
c. Educate your employees
The critical step is giving them cyber security literacy rather than crying over spilt milk. As part of their orientation, they should know to
- Have a strong password for their log-in IDs and change them at frequent intervals.
- No to opening unsolicited mail and clicking on unauthorized links.
- How to report any form of cyber threat.
- Have policies in place to segregate between personnel and official use of company facilities.
d. Guard your equipment and network
- Turn on the spam filters to prevent phishing/scam emails from entering your employees’ email accounts.
- Keep your software updated automatically to prevent benefits from the security upgrades.
- Install a firewall that vanguards between your firm’s network and the Internet.
- Secure all wireless access points and networks
- Delete all information when you dispose of old computers and back up the data.
e. Protect your data
- Keep confidential data and send them on the Internet through an encrypted mode to prevent any form of tampering.
- The top layer of the firm needs dual or multi-layer authorization when accessing financial or other confidential information.
- Have a strong backup of all your digital information transferred to your server intermittently.
How can iSQUARE help you with security?
We live in an interconnected world where all sectors meet at some point before divergence. This meeting point is cyber security which invariably all industries have to adapt and implement. The primary objective of iSQUARE, an ISO 27001-certified organization, is to enable our customers to carry on with their business and take care of their cyber security.
Our years of experience are reinforced to cater to the needs of our clients. Whether it is subject knowledge, customer service or timely solutions, do not hesitate to contact us to help you find the right solutions.