Facing Any of These 7 Security Risks in Mobile Apps? Here is What You Need to do!

We’ve entered the digital age where “mobile apps” are ruling the entire planet. That’s why many entrepreneurs are utilizing this trend effectively by building their own mobile apps. But, when you fail to focus on security while developing your app, then there are more chances of being vulnerable to malicious attacks and the risk of losing your personal information and data.
In this blog, we’ll discuss the types of security threats faced by mobile apps along with the solutions to overcome those threats.
What is Mobile Application Security?
Mobile app security is the process where several types of security features are developed, added, and tested while developing an app. The main purpose of adding security features is to ensure that your app is free from security threats like malware and mishandling of data.
Types of Security Threats and its Solution
Here are the top 7 mobile app security issues that developers witness while building apps. No matter you’re building an Android or iOS app, it’s essential to focus on security to ensure that data is safe and guarded. By understanding these common issues and their solutions, you can ensure that your app is secure on all devices. So, let’s get started.
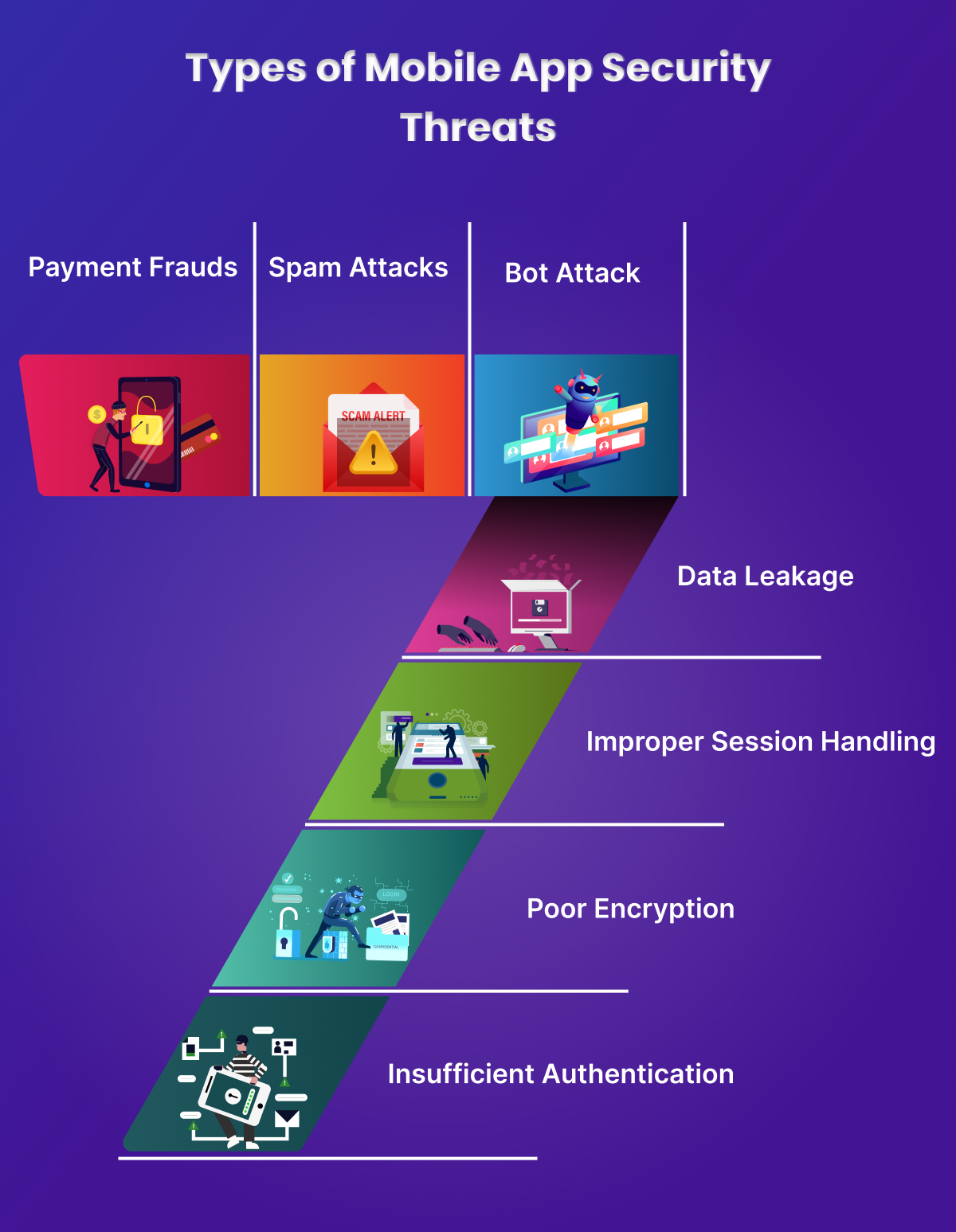
1. Payment Fraud
Payment fraud is any kind of illegal financial transaction that occurs in your app. It includes activities like stolen payment credentials, identity theft, phishing, ATM skimming, QR code scam, and many more. If you own an app, you must ensure that your app comes with powerful payment security features.
Solution
- Associate with a trusted payment partner
- Encrypt all the financial transactions that comprise confidential data
- Regularly examine tokens and login credentials
- Asking for passwords every time the users log in Constantly run security checks with antivirus software
2. Spam Attacks
Spam attacks are nothing but unsolicited and phishing attacks which is a malicious attempt to gain access to your app. A spam or phishing attack occurs when a suspicious user sends a spammy link to a bunch of people and asks them to click the link or download an attachment that will redirect users to get trapped into information theft and hacks.
Solution
- Find out the recent attack methods and create awareness regarding the precautionary steps with the users to avoid potential attacks
- Nowadays, you can find various extensions that enable you to identify the signs of malicious activities in your app
- Adding that additional layer of security with password spinning can prevent upcoming attacks and protects from harmful attacks.
- Installing firewalls helps to enhance your security and decreases the possibility of a hacker cracking your data.
3. Poor API Protection
API is the protocol that is highly crucial while developing an app. A mobile app allows an application. API acts as an intermediary among different applications to communicate with each other. For example, API allows a travel app to take information from diverse hotels, and airline reservations.
As software programming is a bit complicated process as many software projects depend on API integrations to run. However, the challenge in API development relies on the interaction with code you could have missed which essentially needs debugging process.
Solution
To troubleshoot this API error,
- Try to identify which API calls cause the loop
- Increase the standard hosting package
- Optimize the repositories in case of massive page traffic.
- Ensure that you’re sending valid data parameters with your requests
4. Data Leakage
Data leakage is a kind of unauthorised data transmission that occurs within a company to an external source. Unintended data leakage occurs when a developer accidentally provides sensitive information which enables access to other apps on your device. It mainly takes place when source code processes or asks for sensitive data.
Solution
- Prevent data with encryption keys
- Disable cache data
- Regularly monitor the traffic
- Opt for DLP (data leakage prevention) software
5. Improper Session Handling
Improper session handling takes place in the scenario where the session token is unwittingly shared with attackers while the transaction between the app and backend data. There are a few scenarios where session handling goes off the mark.
For instance, when the user logs out from the app, the session or data is deleted from the device, but it is not removed from the server.
Solution
- Meet all authentication and session management requirements defined in OWASP’s security standards.
- Focus on eliminating XSS flaws which can be used to steal session IDs
- Strong efforts should also be made to avoid XSS flaws which can be used to steal session IDs.
- Manually review codes to ensure that your app is free from vulnerabilities.
6. Client-Side Injections
The client-side injection is the output of harmful code on mobile devices on the app. This code is provided in the form of data that the threat agent transfers to the app in different ways. For example, the SQL database of the app will be the focus of hackers to acquire sensitive information from users.
Solution
- Disable strings that contain data from any unauthorized source that is identified as JSON.
- Instead of using the eval () function for analysing JSON data, it is recommended to use JSON.parse to safely prospect JSON response data.
- Ensure that access to the file system is disabled for any app views.
- While designing SQLite queries, make sure that the data supplied has been transmitted to parametrized query.
7. Server-Side Vulnerability
Weak server-side control is a kind of security vulnerability that enables attackers to prompt the server-side app to create a request to an unintended location. There are different types of server-side vulnerabilities which include flaws in code logic, unsecured server configuration, poor authentication rules, access control threats, and so on.
Solution
- Consistent testing and security practices is an effective way to find the newest threat and fix it at an earlier stage.
- Enabling permission-based access control method that the authorization layer investigates if the user has authority to ingress specific data. Also, it checks whether the roles of users will be having specific permission.
- The implementation of the CORS (Cross-Origin Resource Sharing) protocol facilitates a controlled way to share cross-origin resources.
Take Away
Mobile app security is crucial to the success of a mobile app, which is why you need to reach a prominent mobile app development company to thrive among your competitors. Are you looking for an ideal app development partner? Then without any dilemma, reach iSQUARE, the most sought-after app development company which comprises a team of seasoned developers. With 7+ years of experience in app development, we build superlative mobile apps with top-notch features and functionalities. Therefore, get in touch with us to develop a spectacular app for your business!